Breaking eBPF Security: How Kernel Rootkits Blind Observability Tools
Deep technical analysis of bypassing eBPF-based security solutions through kernel-level hooks targeting BPF iterators, ringbuffers, and perf events

Search for a command to run...
Articles tagged with #security
Deep technical analysis of bypassing eBPF-based security solutions through kernel-level hooks targeting BPF iterators, ringbuffers, and perf events

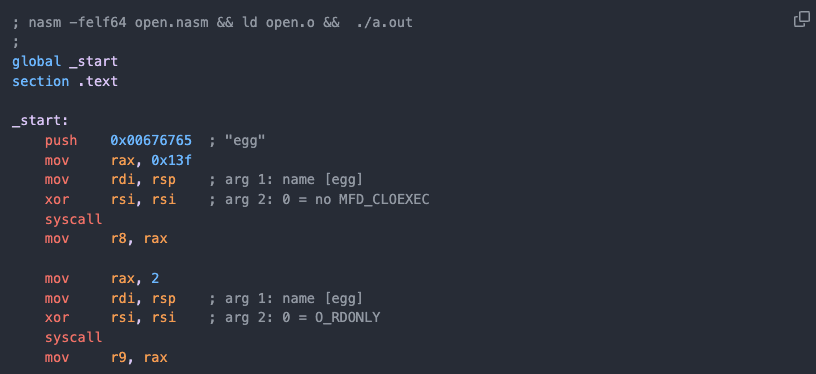
TL;DR: Execute a binary on a Linux system when execution is not allowed (e.g. restricted PHP environment, read-only filesystem or noexec mount flag). By using only Bash and making syscall(2)’s from Bash (!) and piping the ELF binary straight from the...
After reading this article you will be able to start a Debian-Linux (including Kernel) from any (unprivileged) Linux shell. User Mode Linux (UML) is a modified Linux Kernel that the user starts just like any other Linux program. The UML-Kernel then "...

How to run Docker-in-VM-in-Docker on Segfault's Servers

TL;DR: The era of only filtering ingress traffic has come to an end. Differentiating between legitimate and non-legitimate egress traffic is challenging when the attacker uses Cloudflare, Google-drive or AWS. Introduction In this article, you will le...
A short selection of Cloud-based Linux Root Shells and their resource limits. Overview: | MEMORY | STORAGE | CPU | comment ------------------+--------+---------+-----+--------- Github Codespace | 32GB | 8GB | 4 | 20Gpbs Git...