iq.thc.org was hacked? well...
Proof of Concept
Search for a command to run...
Proof of Concept
No comments yet. Be the first to comment.
Deep technical analysis of bypassing eBPF-based security solutions through kernel-level hooks targeting BPF iterators, ringbuffers, and perf events

Abstract Running multiple VPN tunnels on a system has become a de-facto standard on all of my machines since 2+ decades. Historically, these types of tunnels consisted of OpenVPN IPSEC WireGuard During a recent migration effort, I was able to el...
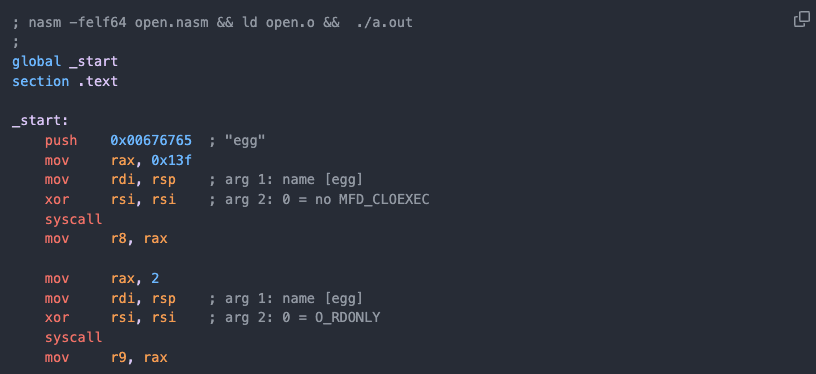
TL;DR: Execute a binary on a Linux system when execution is not allowed (e.g. restricted PHP environment, read-only filesystem or noexec mount flag). By using only Bash and making syscall(2)’s from Bash (!) and piping the ELF binary straight from the...
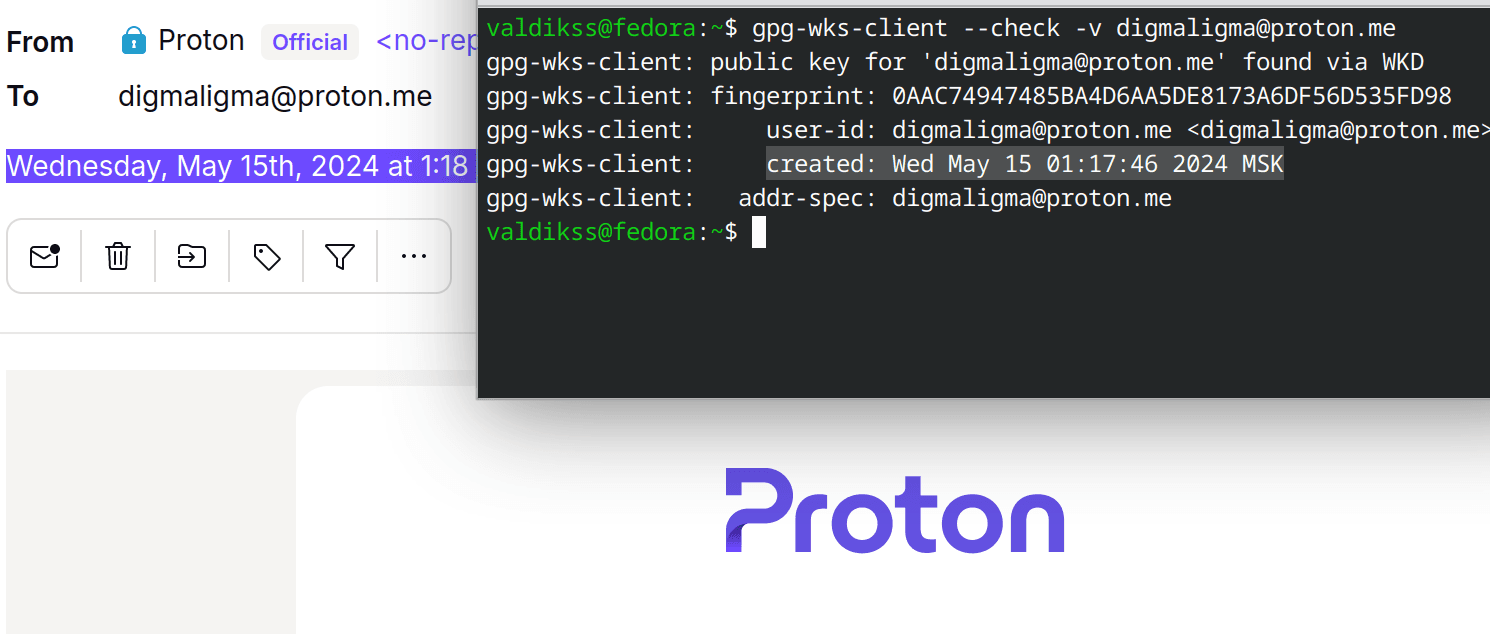
TL;DR: Proton Mail generates PGP key and publishes it upon account creation using Web Key Directory (WKD) standard. The key contains account creation timestamp, with second precision, which reflects the account creation date. Proton, a privacy-orient...
After reading this article you will be able to start a Debian-Linux (including Kernel) from any (unprivileged) Linux shell. User Mode Linux (UML) is a modified Linux Kernel that the user starts just like any other Linux program. The UML-Kernel then "...

Knowledge Base
15 posts