Securing Multi-VPN Access
Abstract
Running multiple VPN tunnels on a system has become a de-facto standard on all of my machines since 2+ decades. Historically, these types of tunnels consisted of
OpenVPN
IPSEC
WireGuard
During a recent migration effort, I was able to eliminate all OpenVPN and IPSEC connections and implemented fresh WireGuard connections into all relevant endpoint networks. However, handling 10+ different tunnels per machine made me think about a mechanism to organize and secure the VPN tunnel buildup and teardown process, and omit potential OPSEC issues introduced by the presence of configuration files as much as possible.
Requirements
We define the following requirements:
Tunnel configs should be stored as secure as possible
Tunnel buildup and teardown should happen nearly automatically
There should be no state where an attacker can access VPN configs
All of the above should be accomplished by using a single command
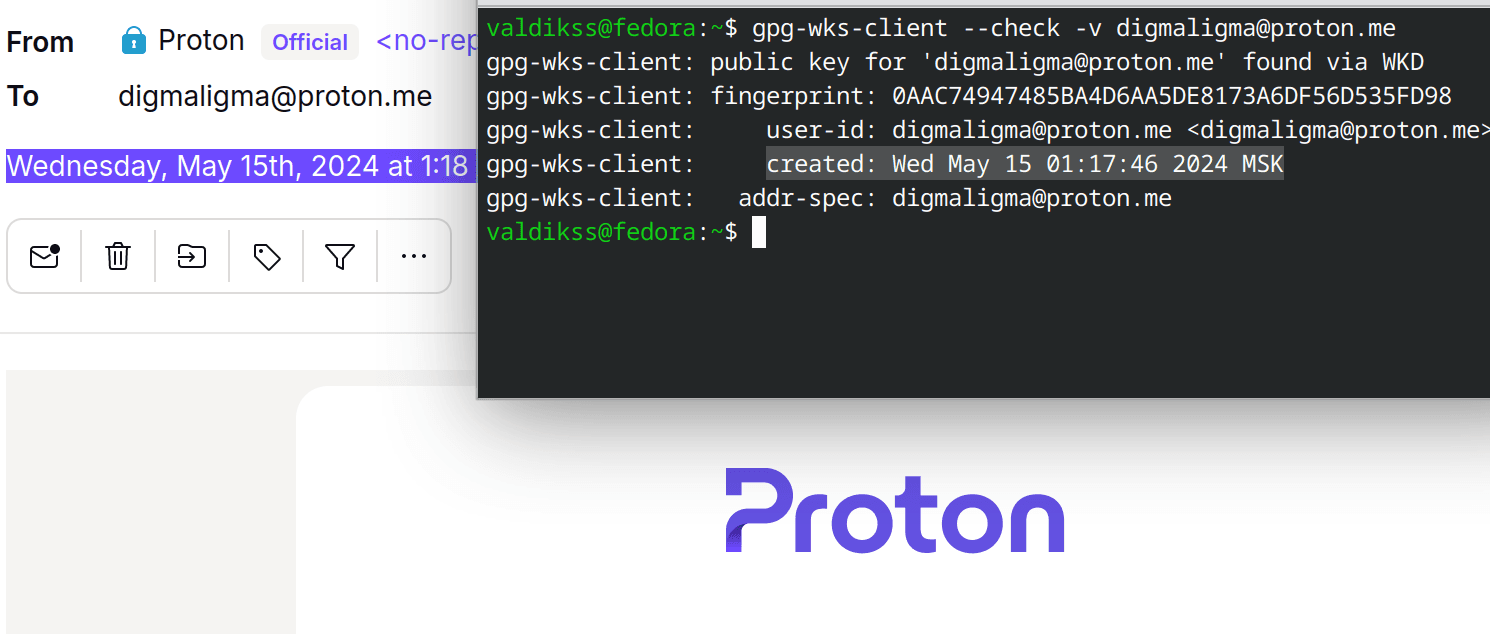
We run FDE on all of our systems, but we like the approach of double-layered security as well, which is why we implement the usage of GPG as well to store an encrypted archive of relevant VPN configurations. This also simplifies redundant storage on potentially insecure media alot.
In the end, we created the following scripts to achieve all of the above:
ADMx Skript
#!/bin/env bash
gpg -d ADMIN0.tgz.gpg > ADMIN0.tgz
tar xvzf ADMIN0.tgz
chmod 600 *.conf
./VPN.sh up
rm -rf *.conf ADMIN0.tgz
exit 0
What this skript does, is:
decrypt the GPG encrypted ADMIN0.tgz.gpg
extract the ADMIN0.tgz archive containing relevant VPN configs
adjust permissions to omit warning messages
establish all tunnels using another skript
remove all plaintext configurations and the archive right after
VPN Skript
This is a simple one-liner to establish VPN connections to all endpoints using available configuration files:
for i in `ls *.conf`; do wg-quick $1 ./$i ; done
As you can see, the skript accepts one option, which is "up" in our example, but could also be "down" to close all established VPN tunnels w/ a single command:
Summary
We are now able to deploy multiple ADMINx folders in our redundant storage, each containing machine specific configurations for all relevant endpoints. Using GPG, we are able to transparently decrypt the configs only for the minimal time they are required for tunnel buildup, and immediately erase them afterwards. All of this enables us to securely establish VPN connections by running a single bash skript on the commandline:
./ADM0.sh